Access Control Systems: Your Solution to Comprehensive Building Security
Sound commercial building access control systems are crucial for safeguarding properties. You will learn how they reinforce a building’s security framework and improve its overall management.
Building security has been of utmost importance and has brought forward new challenges with digital evolution. However, access control remains the essential element of site security. So, what are access controls?
Today, access control transcends the traditional boundaries, extending to controlling access to devices, equipment, and digital entities such as computer files, apart from regulating access to building premises and its various sections. It is here that the role of access control platforms becomes evident.
They offer a level of security that reduces risk by maintaining the security of facilities, data, and people. Working hand in hand with IT security, it ensures that none of your building’s components and its users are exposed to physical and digital security threats. As a result, they play an essential role in managing cybersecurity risks in FM.
This blog will explain how crucial access control systems are for your facility.
Ways How Access Control Systems Guards your facility
You can safeguard assets and property remotely thanks to valuable functionalities like real-time warnings, video surveillance, and remote security access. These solutions usher in a 360-degree transformation by implementing essential security measures.
Now, you might wonder, “Why use building access control systems?” The answer lies in the six benefits they bring to your organization:
1. Bringing Restrictions
One of the key benefits of property access applications is the ability to restrict access to specific areas or rooms within a site. This ensures that only authorized personnel can enter those areas, reducing the risk of unauthorized access, theft, or other criminal activities, thereby protecting sensitive information and valuable assets.
For instance, access control applications restrict access to a facility’s data center that stores sensitive information.
It can be programmed to grant access to authorized personnel at specific times, days, or frequencies. By doing so, access can be limited to only the required areas during necessary times. Managers can program it to grant access to their employees only during business hours or to allow the cleaning staff entry only at the end of their shift.
2. Activity Monitoring
Access control for commercial buildings lets you watch who enters and exits a property. Managers can use the information to identify suspicious activity, such as attempts to gain access outside of business hours or during times when an employee should not be on the premises. By monitoring access activity, you can detect and prevent potential security threats.
Most importantly, commercial or residential solutions can be integrated with video surveillance applications to provide a complete picture of what is happening at the site. The video footage can be accessed and reviewed in real-time or retrospectively during an incident.
3. Safety Enhancement
The importance of access control becomes evident when considering how it enhances the safety and security of a property. Access control solutions play a crucial role in safeguarding occupants and assets by strategically limiting access to certain areas.
For instance, managers can use access control solutions to restrict access by staff members to guest rooms. Similarly, a hospital may use it to limit access to areas containing hazardous materials or sensitive medical equipment.
It enables quick and easy evacuation in case of an emergency. When the fire alarm rings, the access control software can automatically unlock all doors to facilitate evacuation. This is especially important in large premises where manually opening doors can take time and delay evacuation.
4. Centralizing Control
Another significant benefit of access platforms is that they provide centralized control to enforce consistent access policies across an organization. This means that access permissions can be set and adjusted based on a user’s role, responsibilities, and level of trust within the organization.
Centralized control also provides real-time monitoring and reporting capabilities, allowing organizations to track who has accessed specific resources. This information can be used to identify potential security breaches or suspicious activity, enabling organizations to respond quickly and prevent further damage.
Finally, centralized control allows for scalability and flexibility. As organizations grow and their access control needs change, centralized management makes it easy to add or remove users, modify access permissions, and integrate with other security systems for buildings.
5. Improving response times
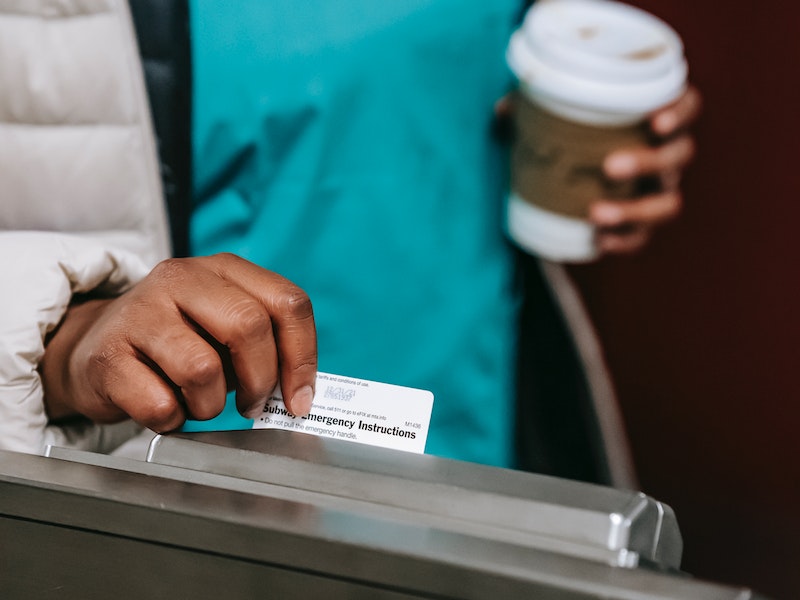
Access control solutions are security measures that restrict entry to specific areas or properties to authorized personnel only. These applications can include methods such as key cards, biometric scanners, and passwords.
It can improve response times in several ways. Firstly, it allows a quick and efficient way to identify who is authorized to enter a property or specific area instead of manually verifying each person’s identity. Security personnel can focus on those without authorized access, increasing the chance of detecting and responding to potential threats.
Secondly, the solution can provide real-time monitoring of entry and exit points, allowing security personnel to quickly respond to security breaches or suspicious activity. This can be especially helpful in large sites or areas with multiple entry points, where keeping track of who is coming and going can be challenging.
6. Effectively dealing with emergency
In a fire emergency at large commercial sites in New York City in 2020, access control software allowed managers to lock down specific areas and evacuate individuals quickly and safely through designated exit routes. This helped ensure the safety of employees and visitors and minimized the risk of injury or loss of life.
In Texas in 2018, in a school shooting incident, an access control system allowed the school to quickly lock down the property, preventing the shooter from entering other areas and potentially causing more harm. It also allowed emergency responders to immediately access the property to assist the injured.
These real-life examples illustrate how integrating access control solutions, including commercial door entry security systems, seamlessly into emergency preparedness protocols can significantly enhance the ability of security personnel and first responders to react swiftly and effectively during critical situations.
Conclusion
We hope, by now, you might have understood how vital access control platforms are in facilities management (FM). The advantages of FM for building operations are many. The advantages of FM for site operations are many, and you get the added benefit of building security devices into your system, creating a solid security layer that significantly reduces the chances of security breaches.
With a sound access control application, you can provide users restricted, shared, or personal access to the site and IT resources like web services or locally installed password-protected files.
While implementing access control platform, the primary consideration should be ensuring that they enable you to follow accepted standards and practices.
With facility management software, we have assisted our clients in building robust access control systems through our facility application. It is tailored to incorporate the client’s security requirements, enhancing authentication and allowing for controlling user privileges. Get in touch with us today to understand more from our experts.


